Future Trends in Concrete Saw Blade Design and Manufacturing
The construction equipment sector is experiencing a massive wave of technological innovation, driven by global demands for safer working conditions, higher project efficiency, and strict carbon emission regulations. In the field of high-volume masonry modification and flatwork cutting, traditional brute-force production methods are giving way to advanced digital material sciences and automated molecular engineering. Today’s…
Complete Watch Care Guide for Certified Pre-Owned Timepieces
Understanding the Value of Your Watch Investment A watch is more than a timekeeping device; it is a long-term investment, a style statement, and often a piece of craftsmanship passed down through generations. When you own pre-owned luxury watches Los Angeles collectors often seek, you are holding a timepiece that has already been inspected, authenticated,…

A Deep Dive into the Features of the hemi pharma official website
Introduction to the hemi pharma official website The hemi pharma official website serves as a central digital platform designed to provide information about pharmaceutical products, company updates, and healthcare solutions. In today’s digital healthcare era, pharmaceutical companies rely heavily on official websites to communicate directly with patients, healthcare professionals, and distributors. The hemi pharma official…

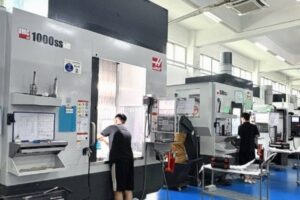
Top Advantages of Choosing CNC Machining China for High-Quality Production
Understanding the Growing Demand for CNC Machining China In today’s highly competitive manufacturing industry, precision, efficiency, and cost-effectiveness are essential for success. This is where CNC Machining China has become a leading solution for businesses across the globe. Companies from automotive, aerospace, electronics, medical devices, and industrial equipment sectors increasingly rely on CNC Machining China…

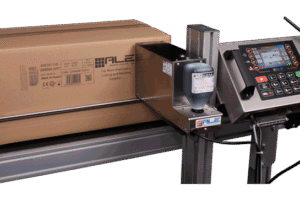
Why Businesses Are Switching to TIJ Inkjet Printer Technology for Product Marking
In today’s highly competitive manufacturing and packaging industries, accurate product marking has become more important than ever. Businesses need reliable solutions for printing batch numbers, expiration dates, barcodes, QR codes, logos, and traceability information on a wide range of products and packaging materials. As production demands continue to evolve, many companies are moving away from…

Top Innovations Every Trampoline Park Equipment Manufacturer Is Bringing to Modern Parks
The trampoline park industry has evolved rapidly over the past decade. What began as a simple collection of interconnected trampolines has transformed into a highly interactive entertainment destination that attracts visitors of all ages. As customer expectations continue to rise, every Trampoline Park Equipment Manufacturer is focused on delivering innovative solutions that improve safety, enhance…

A Complete Beginner’s Guide to Understanding 竞技宝 Platform Features
Introduction to 竞技宝 and Its Digital Ecosystem The digital entertainment industry has evolved rapidly, and platforms like 竞技宝 have become increasingly recognized among users who are interested in interactive online experiences. For beginners, understanding how 竞技宝 works can feel overwhelming at first, especially with the variety of features, tools, and user interfaces involved. However, once…
How Medical Thai Massage Supports Pain Management and Physical Recovery
Understanding the Healing Power of Medical Thai Massage Medical Thai massage is a structured therapeutic practice that combines assisted stretching, acupressure, and deep tissue manipulation to support the body’s natural healing processes. Unlike general relaxation massage techniques, medical Thai massage is designed with a clinical approach, focusing on specific health concerns such as chronic pain,…
How a Modern Math Solver Can Improve Daily Practice and Exam Preparation
Mathematics is one of the most important subjects in education, but it is also one of the most challenging for many students. From basic arithmetic to advanced calculus, learners often struggle to understand formulas, solve equations, and complete assignments on time. In today’s digital world, technology has transformed the learning experience, and one of the…
Jillian Michaels Gelatin Recipe: A Simple Way to Boost Wellness and Lose Weight
The growing popularity of natural wellness foods has encouraged many health-conscious people to search for simple recipes that support weight management, digestion, and overall vitality. One trending option is the https://www.youtube.com/watch?v=qemWt5cGO7c , a nutritious and easy-to-make wellness drink that combines the benefits of gelatin with healthy lifestyle habits. Known for promoting fitness and clean eating,…